Person on U.S Secret Service's Most Wanted Cybercriminals List and U.S Sanctions List Runs a Profitable Managed Android Malware Enterprise - An OSINT Analysis
Introduction to WHOIS XML API
WhoisXML API is one of the Web’s and the security industry’s primary destinations for threat intelligence and cybercrime research including OSINT type of domain, IP, and current and historical WHOIS data records with billions of domain IP and WHOIS records within WhoisXML API’s database where novice and experienced cybercrime researchers threat intelligence analysts including OSINT experts and analysts should consider adopting WhoisXML API’s in their arsenal of OSINT tools and public database repositories and databases largely considering the tool as their primary information source and threat intelligence gathering tool and publicly accessible database in terms of using it in their current and ongoing OSINT and cybercrime including threat intelligence type of investigations.
How to get a proper account
Cybercrime researchers and threat intelligence analysts interested in obtaining access to one of the Web’s and the industry’s most comprehensive and in-depth data set of real-time and historical domain IP and WHOIS information should grab an account from the following URL - https://main.whoisxmlapi.com/signup in order to begin their OSINT and cybercrime research including their threat hunting and threat intelligence gathering process.
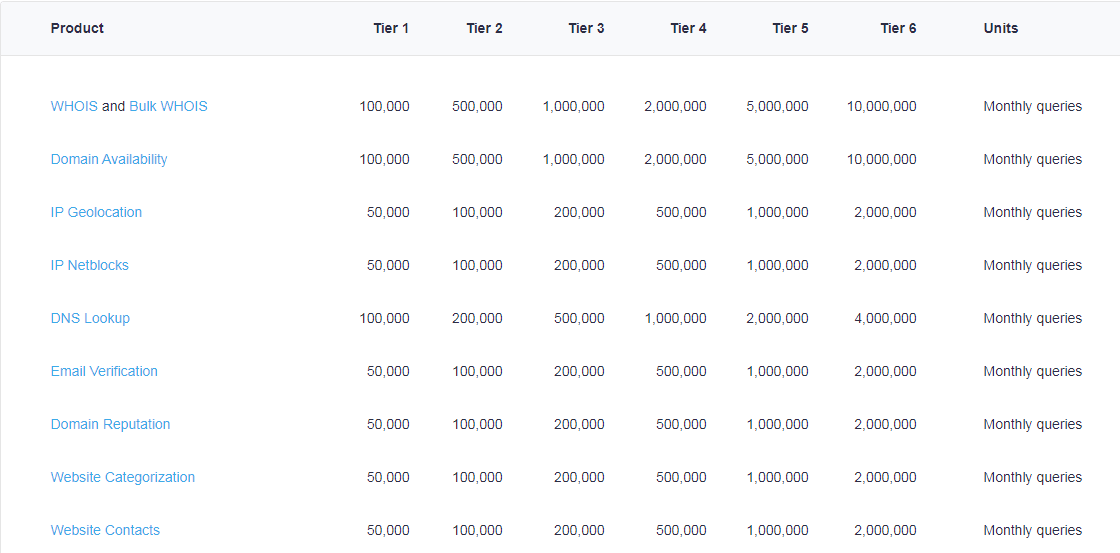
Sample WhoisXML API Pricing Plans Web Site
How to install Maltego
For the purpose of this case study we’ll use the popular OSINT gathering and enrichment tool Maltego, which you can grab from the following URL - https://www.maltego.com/downloads/ to begin using and utilizing WhoisXML API’s advanced domain, IP, and historical and current WHOIS information and one of the Web’s and the industry’s most comprehensive and in-depth databases.
Sample Maltego Download Web Site
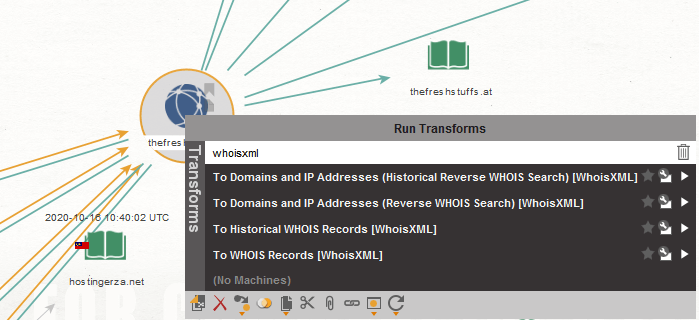
How to use the WHOIS XML API Maltego Integration
Before using Maltego users should follow the instructions and grab a proper WhoisXML API account which they can later on use for the actual research and OSINT research and analysis, including the actual enrichment process.
The Case Study
We’ve recently decided to take a look at the U.S Secret Service’s Most Wanted Cybercriminals list which we closely monitor and track for new developers for the purpose of using basic OSINT techniques on our way to attempt to track down and collect and present personally identifiable information including technical details behind one of the U.S Secret Service’s Most Wanted cybercriminals and we succeeded in doing that by finding out and providing additional information on one of their Web properties which is basically a managed Android malware enterprise.
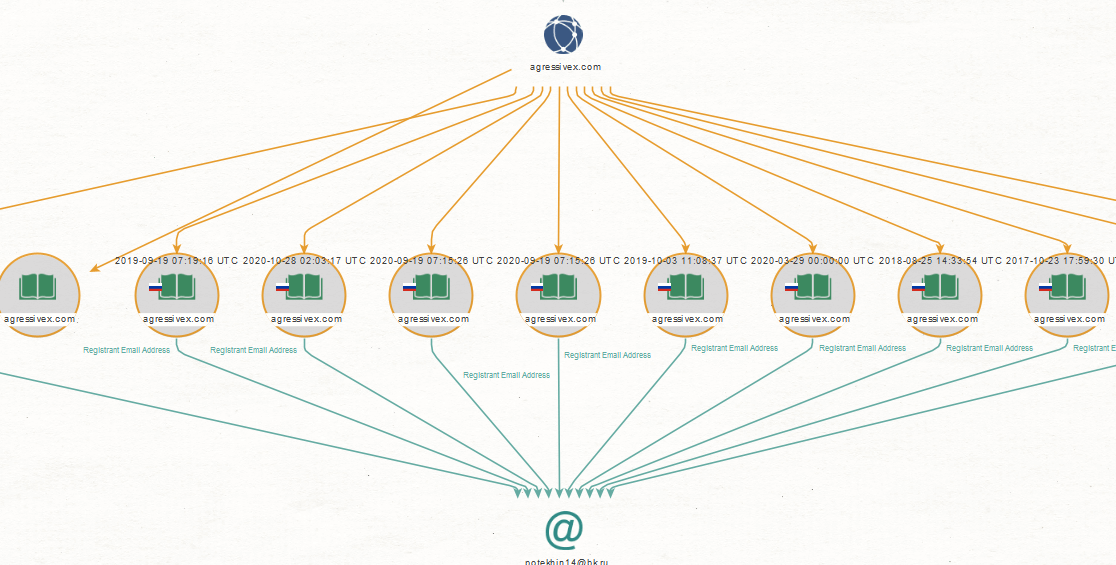
In this post we’ll offer practical and technical cyber attack attribution detail on Danil Potekhin who is on the U.S Secret Service Most Wanted Cybercriminals list in terms of the online infrastructure he’s currently running with the idea to assist U.S Law Enforcement on its way to track down and prosecute the cybercriminals behind these campaigns.
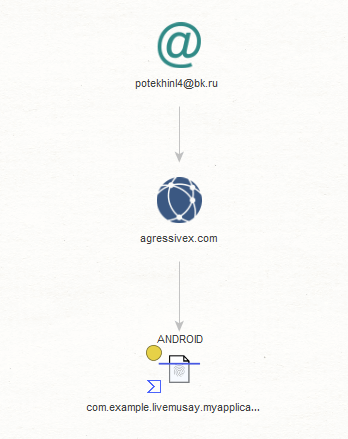
Sample web site he’s currently running which is basically a managed Android malware botnet enterprise: hxxp://agressivex.com
Sample personal email which we found out using OSINT techniques and used for the purpose of this case study: [email protected]
We’ll continue monitoring the campaign and post updates as soon as new developments take place.
Read other articles


































